This code hacks nearly every credit card machine in the country
Get ready for a facepalm: 90% of credit history card readers now use the identical password.
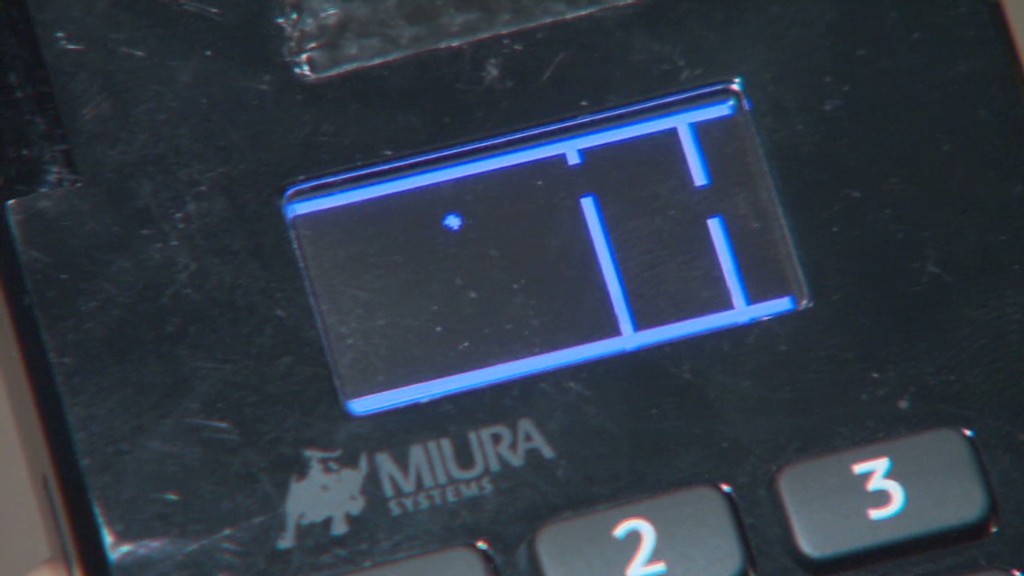
The passcode, set by default on credit rating card devices considering the fact that 1990, is easily found with a swift Google searach and has been exposed for so lengthy there is no feeling in making an attempt to disguise it. It really is either 166816 or Z66816, depending on the machine.
With that, an attacker can achieve finish handle of a store’s credit history card viewers, possibly permitting them to hack into the equipment and steal customers’ payment details (believe the Target (TGT) and Home Depot (High definition) hacks all over all over again). No question massive retailers continue to keep shedding your credit card info to hackers. Safety is a joke.
This newest discovery arrives from scientists at Trustwave, a cybersecurity business.
Administrative access can be employed to infect devices with malware that steals credit card information, stated Trustwave executive Charles Henderson. He specific his findings at very last week’s RSA cybersecurity convention in San Francisco at a presentation identified as “That Stage of Sale is a PoS.”
Acquire this CNN quiz — find out what hackers know about you
The trouble stems from a recreation of sizzling potato. System makers sell equipment to exclusive distributors. These sellers offer them to stores. But no just one thinks it is really their task to update the master code, Henderson informed CNNMoney.
“No one is altering the password when they established this up for the 1st time all people thinks the stability of their level-of-sale is a person else’s accountability,” Henderson explained. “We are earning it pretty straightforward for criminals.”
Trustwave examined the credit score card terminals at a lot more than 120 suppliers nationwide. That contains significant garments and electronics outlets, as perfectly as regional retail chains. No unique suppliers ended up named.
The huge the vast majority of machines ended up designed by Verifone (Pay back). But the similar problem is current for all significant terminal makers, Trustwave explained.

A spokesman for Verifone mentioned that a password by itself is not more than enough to infect machines with malware. The enterprise reported, right until now, it “has not witnessed any assaults on the safety of its terminals based on default passwords.”
Just in scenario, although, Verifone said suppliers are “strongly advised to improve the default password.” And presently, new Verifone gadgets come with a password that expires.
In any scenario, the fault lies with suppliers and their exclusive suppliers. It is really like residence Wi-Fi. If you obtain a property Wi-Fi router, it is up to you to modify the default passcode. Merchants should really be securing their very own machines. And equipment resellers really should be encouraging them do it.
Trustwave, which allows guard merchants from hackers, reported that preserving credit card machines safe is small on a store’s listing of priorities.
“Corporations devote a lot more income choosing the coloration of the position-of-sale than securing it,” Henderson mentioned.
This problem reinforces the summary designed in a current Verizon cybersecurity report: that retailers get hacked since they’re lazy.
The default password factor is a serious problem. Retail laptop networks get exposed to computer viruses all the time. Consider a person scenario Henderson investigated recently. A horrible keystroke-logging spy application finished up on the personal computer a retail outlet works by using to course of action credit rating card transactions. It turns out workers experienced rigged it to perform a pirated edition of Guitar Hero, and unintentionally downloaded the malware.
“It reveals you the level of accessibility that a large amount of persons have to the position-of-sale ecosystem,” he stated. “Frankly, it can be not as locked down as it ought to be.”
CNNMoney (San Francisco) Initial revealed April 29, 2015: 9:07 AM ET